Most cyber attacks never make the news. The ones that do are usually the big, dramatic ones involving well-known brands. They grab headlines, but also hide a bigger reality.
Cybercrime hits small businesses every single day.
Behind closed doors, owners face the same chaos as big companies. The stress. The downtime. The frantic scramble to recover data or get systems back online. For some, the financial damage is enough to drive them out of business.
And here’s the part many business owners don’t always realise.
You don’t need to be a big company to be a target. You just need to be connected to the internet.
In this guide, we’re going to cut through the noise and show why cyber insurance matters, what risks actually look like and how you can protect your business.
Big Names, Bigger Lessons
In recent years, big brands like Jaguar Land Rover and Marks & Spencer were hit by major cyber attacks. Both had specialist IT teams and significant security budgets, yet both were still caught out.
The details differ, but the pattern is the same.
- A stolen password.
- A supplier with weak security.
- A moment of human error.
That is all it takes.
JLR reportedly had no cyber insurance, leaving it exposed to huge losses.
M&S did have cyber insurance, which helped them recover faster after a serious ransomware attack.
Two Attacks. Two Outcomes. One Key Difference
The real lesson is simple.
If global organisations with large budgets and layers of protection can be blindsided, smaller businesses cannot afford to believe they are too small to target.
In the end, the numbers speak for themselves. JLR reportedly suffered billions in disruption, lost production and recovery costs – with no cyber insurance in place.
M&S, on the other hand, filed a £300 million cyber insurance claim that helped them recover quickly and limit long-term damage.
Put yourself in their shoes. Would you rather face a cyber attack with expert support and cyber insurance behind you, or without?
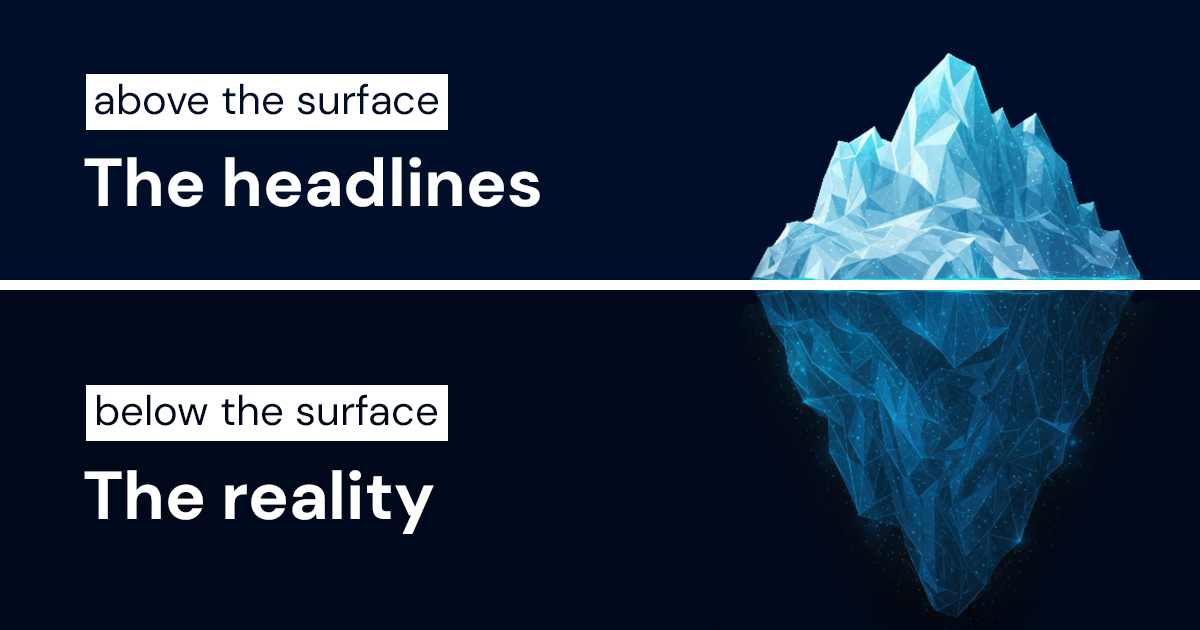
The Hidden Side of Cyber Attacks
What you see in the news is just the tip of the iceberg.
And below the surface, thousands of small businesses are hit with attacks that never make the headlines.
Why Small Businesses Should Pay Attention
The lessons from JLR and M&S don’t just apply to big corporations. They’re a warning for every business that uses email, handles customer data, or relies on suppliers. In other words… everyone!
For hackers, SMEs are low-hanging fruit.
- Fewer defences.
- Fewer IT professionals.
- Fewer checks.
According to the UK Government Cyber Security Breaches Survey, 43% of UK businesses experienced a cybersecurity breach or attack in the last 12 months (30% for charities).
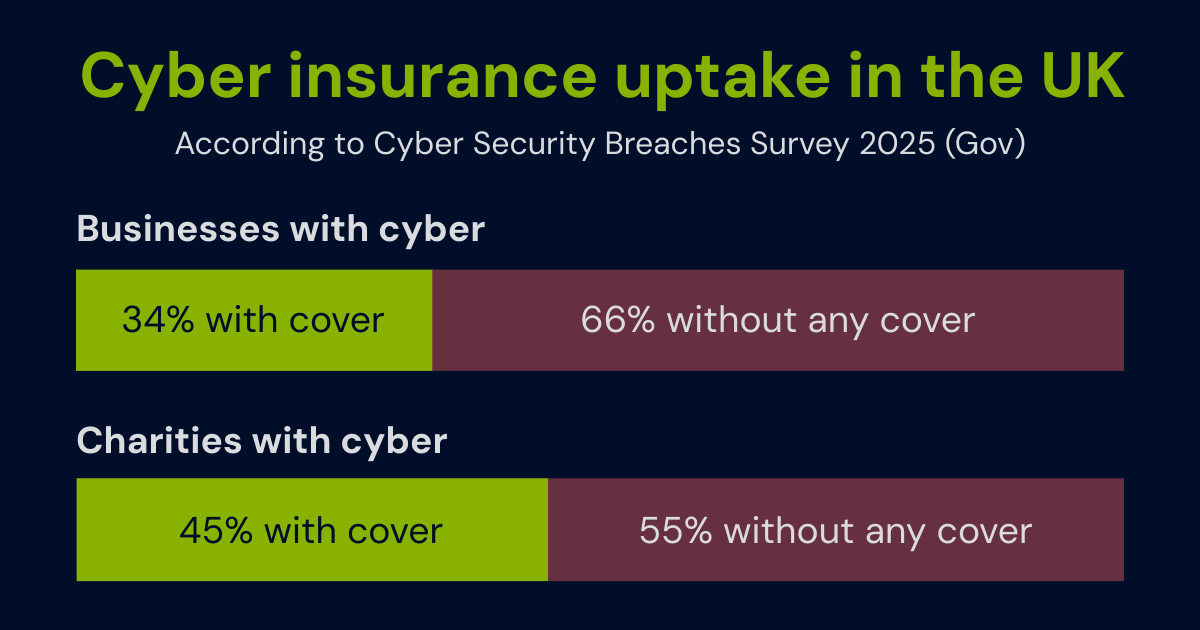
Yet despite this, only 34% of UK businesses have any form of cyber insurance (45% for charities)…
…and just 7% of UK businesses have a dedicated cyber policy at all (5% for charities). In other words, most firms are trying to protect themselves with cover that was never really designed for cyber risks in the first place.
Many business owners assume their existing insurance might extend to cyber risks, such as office policies, liability insurance or even professional indemnity. In reality, these policies are designed to cover very different types of risk.
Cyber incidents require specialist cover, as traditional policies are not designed to respond to events like hacking, ransomware or data breaches.
That gap in protection can have serious consequences.
According to the UK Government’s Cyber Security Breaches Survey, 43% of UK businesses and 30% of charities reported experiencing a cyber security breach or attack in the past 12 months, affecting an estimated 612,000 businesses and 61,000 charities.
Those aren’t distant statistics. They represent local trades, retailers, and professional firms just like yours.
The scale of the threat is growing, but awareness hasn’t kept up. Many small business owners still think cybercrime is something that happens to “the big guys”. The truth is that attackers often choose the path of least resistance.
And for many small businesses, that path leads straight through the front door, not because of weak systems, but because of simple mistakes.
The Path of Least Resistance
Modern cybercrime is based on ease, not effort. Criminals rarely need to “hack” their way in anymore. They simply buy or steal credentials that already exist, knowing that people will reuse passwords.
IBM’s Cost of a Data Breach Report 2025 found that stolen or compromised credentials are one of the most common causes of breaches, responsible for almost one in five attacks worldwide.
Think about that. Not a sophisticated exploit. Not a cutting-edge virus. Just a password that was never changed.
Billions of usernames and passwords circulate on the dark web, many tagged with company domains like @yourbusiness.co.uk. Hackers use automated tools to test these credentials across thousands of websites in minutes, a technique known as credential stuffing.
It’s quick, cheap, and quiet. Attackers don’t need to break down your IT defences when they can simply walk through an unlocked door.
For small businesses, that means your biggest risk may not be a lack of technology but a lack of awareness.

This is the point where many small businesses realise they’re far more exposed than they thought.
If you want to check one simple thing right now, try your business email on Have I Been Pwned. It shows whether your email address appears in known data breaches. It’s quick, free, and gives you instant visibility of compromised accounts.
Simply visit haveibeenpwned.com, enter your email address and click search. It won’t tell you everything, but it is a good place to start.
For deeper insight across your whole business, we include a Free Cyber Risk Assessment when you request a cyber quote.
Phishing: Where Most Cyber Attacks Begin
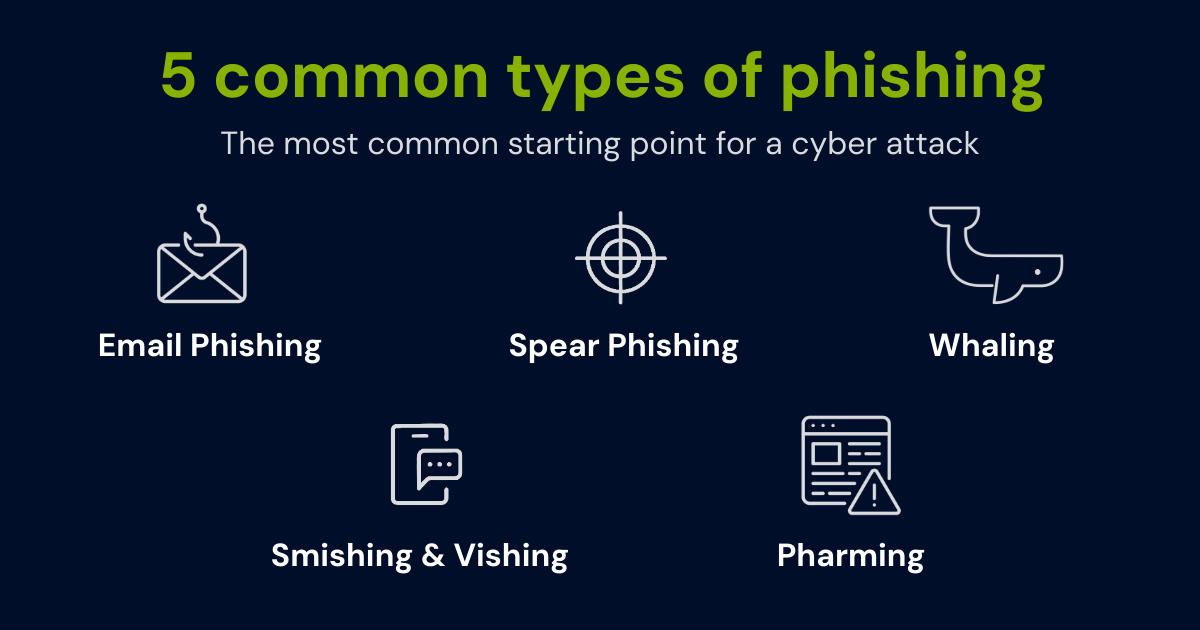
Phishing remains the most common method for attackers to gain unauthorised access.
It requires almost no technical skill — just tricking someone into clicking a link or handing over a password. One click can give an attacker everything they need.
Attribution, icons created by Nawicon from Noun Project
And phishing comes in more than one form. Here are the 5 types of phishing often used by hackers:
- Email phishing: the classic fake email, often pretending to be a supplier, bank or internal colleague.
- Spear phishing: highly targeted messages tailored to a specific person, often based on public information.
- Whaling: going after senior managers or directors by convincing, impersonating bosses or other managers.**TWEAK*
- Smishing & vishing: phishing attempts delivered via SMS text messages or phone calls, often posing as banks, couriers or IT support.
- Pharming: redirecting users to fake websites that look identical to the real thing to steal logins or payment details.
Phishing works because it targets people, not systems. People are often busy, distracted, or simply trying to get through the day. That’s why attackers rely on it.
The Most Dangerous Assumption: “Our IT Handles That”
Whether outsourced or handled internally, many business owners believe their IT provider will keep them safe with firewalls, antivirus, and backups.
But technology only manages part of the risk. The rest depends on people, and people make mistakes.
One forgotten update. One reused password. One misplaced click. That’s all it takes. In fact, human error is the cause of 95% of all cybersecurity breaches, according to Mimecast.

If it’s anything like the JLR and M&S incidents, it might not even be you; it could be a third-party supplier or contractor.
When a breach hits, your IT company can help fix systems, but they won’t pay for lost income, legal costs, or reputational damage.
Why Cyber Insurance Matters More Than Ever
Cyber attacks are no longer rare, complex events. They’re frequent, fast, and almost always financially damaging.
Even with strong IT support, the costs fall on you, not your IT provider.
That’s where cyber insurance steps in.
How Cyber Insurance Helps
Cyber insurance isn’t just another product. It’s the financial lifeline that keeps your business afloat when everything else fails.
When a cyber attack strikes, it can cover the costs that would otherwise come straight out of your pocket:
Practical Steps to Improve Cyber Security
Whilst no checklist can guarantee immunity from cyber attacks, these quick wins can drastically lower your risk, and even help to unlock better rates for cyber insurance.
- 1
Use unique, complex passwords and update them regularly.
- 2
Enable multi-factor authentication (MFA) wherever possible.
- 3
Train your team to spot phishing and suspicious messages.
- 4
Back up data securely and test your recovery process.
- 5
Audit supplier access. Old logins are an easy way in.
Combine these steps with robust Cyber Insurance, and you’ll be prepared both to prevent and to recover from an attack.
Every Business Is A Target
Cybercrime doesn’t discriminate. JLR may have believed they were too advanced to fall. Many small businesses believe they’re too small to target. Both are wrong.
No system is flawless. No company is invisible. The only difference is how quickly you recover when it happens.
Most businesses only realise they need cyber insurance after they’ve been hit, when it’s already too late to buy it. The best time to prepare is before an attack, not in the middle of one.
Take control, protect your business now. Secure your future before a breach happens.
Request a callback
Start your free quote and take control of your cyber risks